
Plausibly Deniable Data Protection Setup

In this tutorial we're going to look at how you can backup your critical data (Keepass accesses, pgp key, ssh key, etc) while still maintaining the plausible deniability.


In this tutorial we're going to look at how you can backup your critical data (Keepass accesses, pgp key, ssh key, etc) while still maintaining the plausible deniability.
source: https://anonymousplanet.org/guide.html#understanding-hdd-vs-ssd
regarding wear leveling:
"Also as mentioned earlier, disabling Trim will reduce the lifetime of your SSD drive and will significantly impact its performance over time (your laptop will become slower and slower over several months of use until it becomes almost unusable, you will then have to clean the drive and re-install everything). But you must do it to prevent data leaks that could allow forensics to defeat your plausible deniability. The only way around this at the moment is to have a laptop with a classic HDD drive instead."
First install veracrypt in the plausibly deniable whonix VM (for more details on how to set that environment up in this previous tutorial), go there to download the latest .deb package:
wget https://launchpad.net/veracrypt/trunk/1.26.7/+download/veracrypt-1.26.7-Debian-12-amd64.deb
dpkg -i veracrypt-1.26.7-Debian-12-amd64.deb
apt install -f
dpkg -i veracrypt-1.26.7-Debian-12-amd64.deb
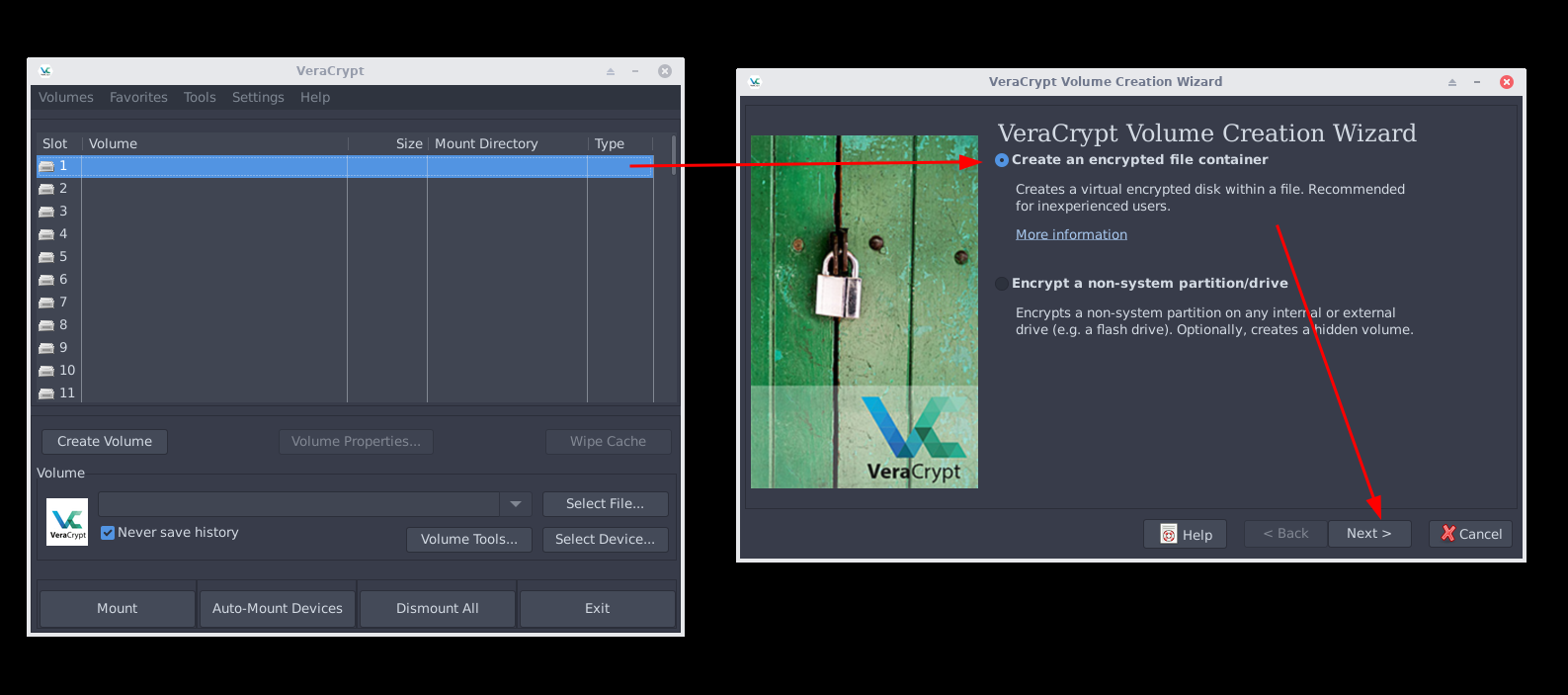
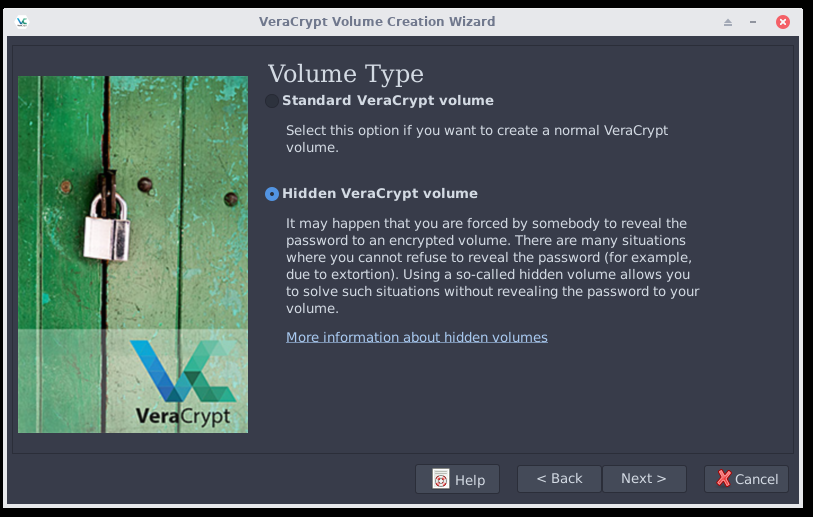
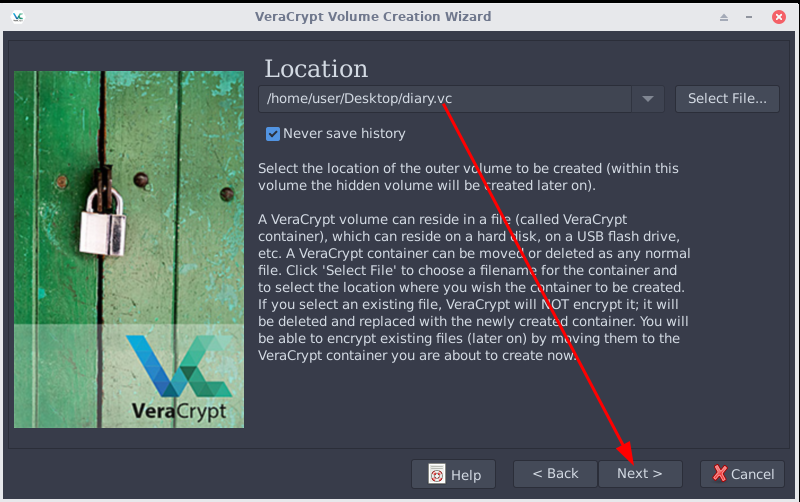
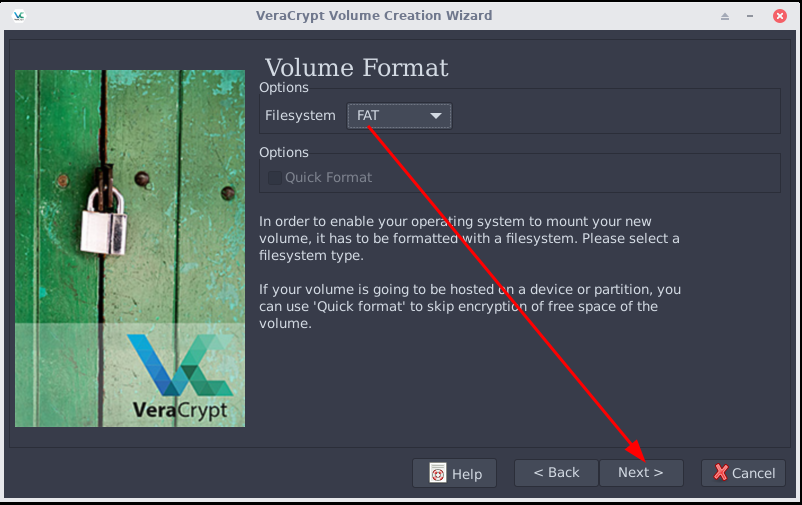
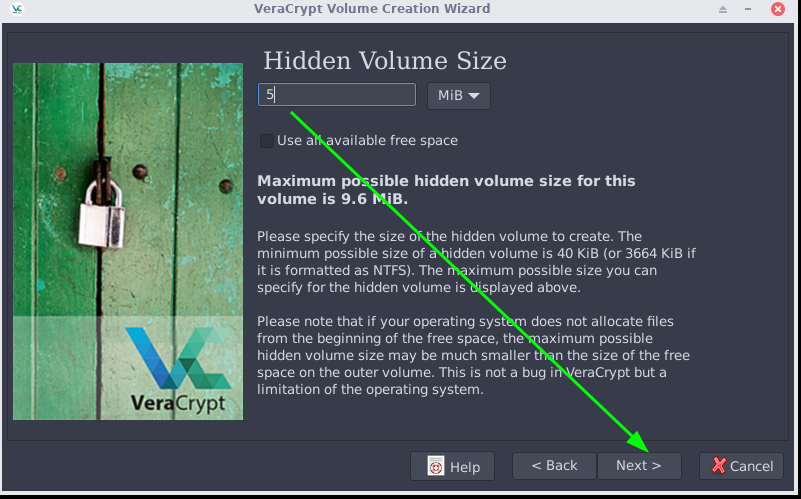
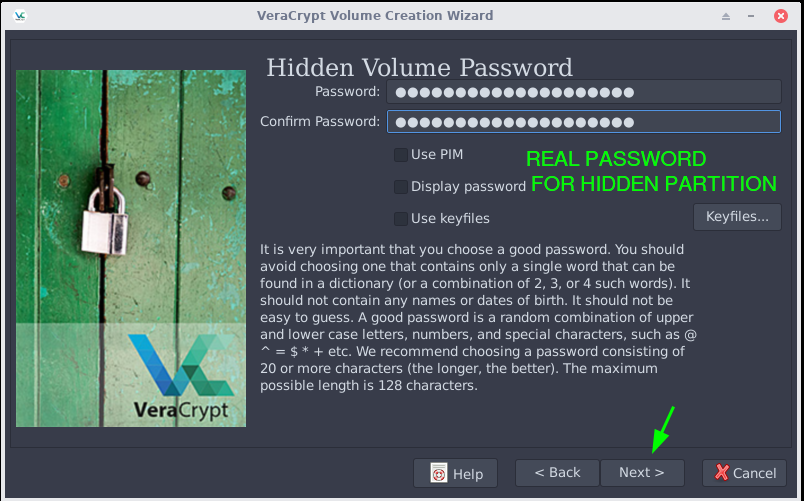
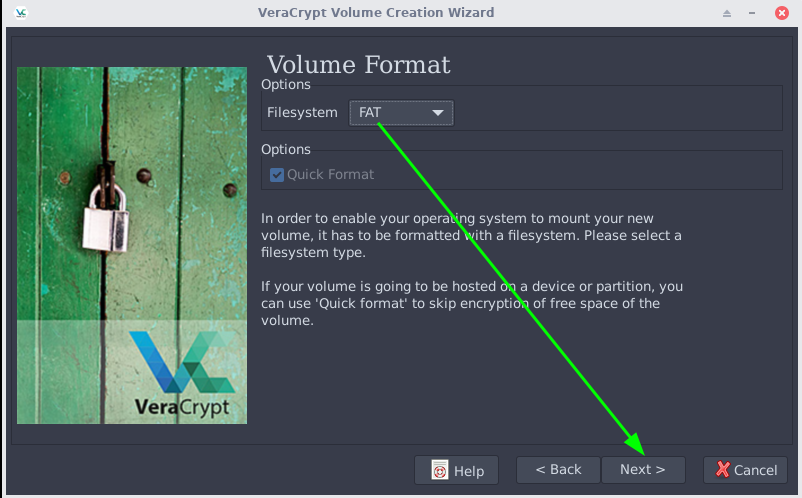
Once veracrypt is setup, we're going to create a small volume with a hidden partition, which will contain all of your critical data, and the decoy partition will contain a weekly diary.
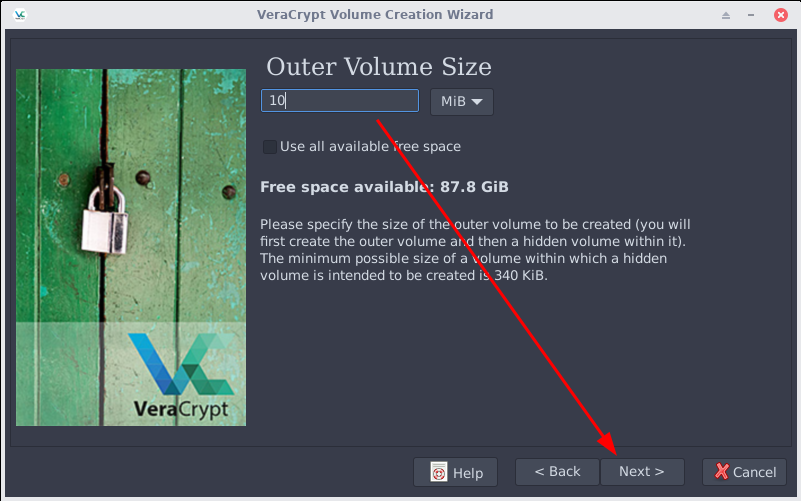
So let's create the volume, we want to keep the size to be low so that it will contain only the critical information.
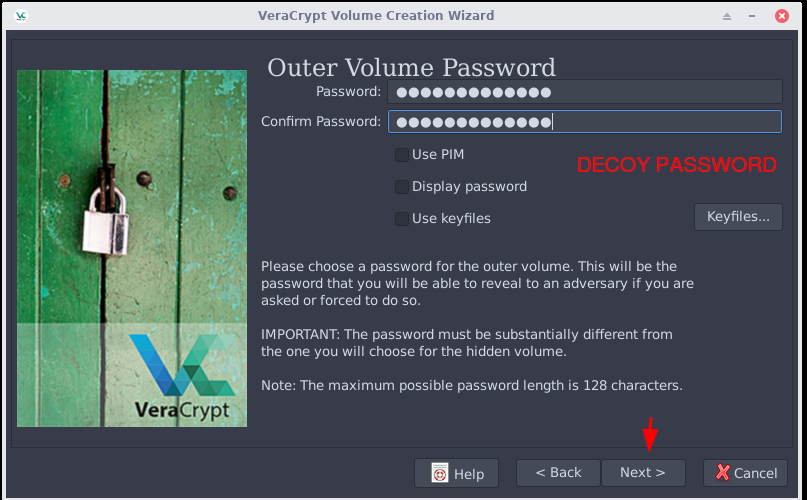
Note: It is important to make sure that the decoy partition is changed everytime the hidden partition is changed, because as it is detailed here it is not advised to backup veracrypt drives online because cloud services almost always retain history of files, meaning if you give your decoy password to all of the previous veracrypt file versions, it must justify that the entire container is different. If the entire container is different while the decoy partition is the same, it means that an adversary can prove that there is a hidden partition. Hence there needs to be a procedure as to how you backup your veracrypt volume online.
Weekly procedure to backup your critical data:
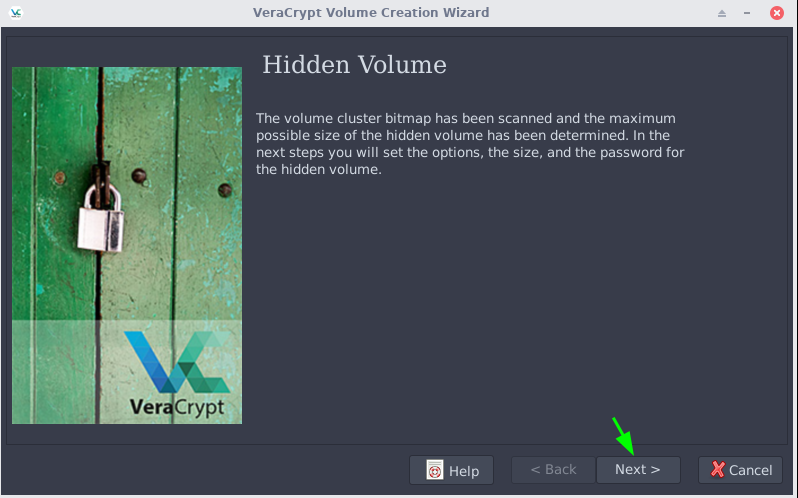
-open the hidden volume of the veracrypt volume diary.vc
-backup all of your critical data (ssh config, ssh keys, pgp keys, keepass .kdbx files, etc.) (max size= 10Mb)
-close the hidden volume
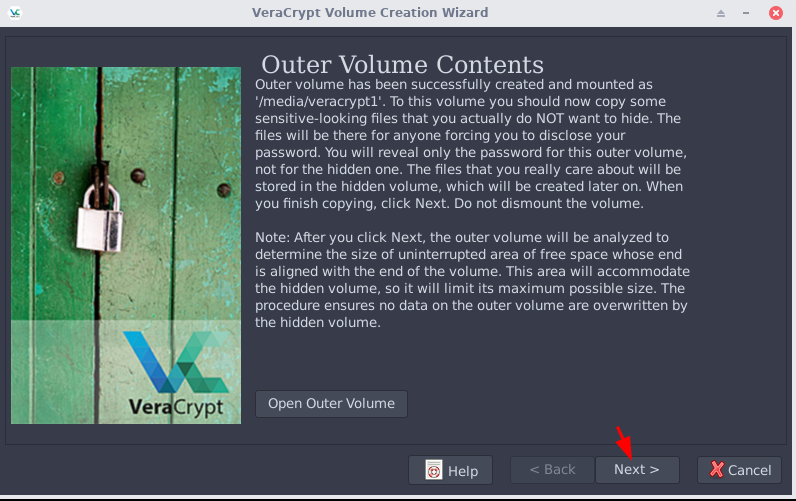
-open the decoy volume of the veracrypt volume diary.vc
-recap your week in a small text file, name it with today's date. (don't reveal the presence of a hidden file in the text content)
-close the decoy volume
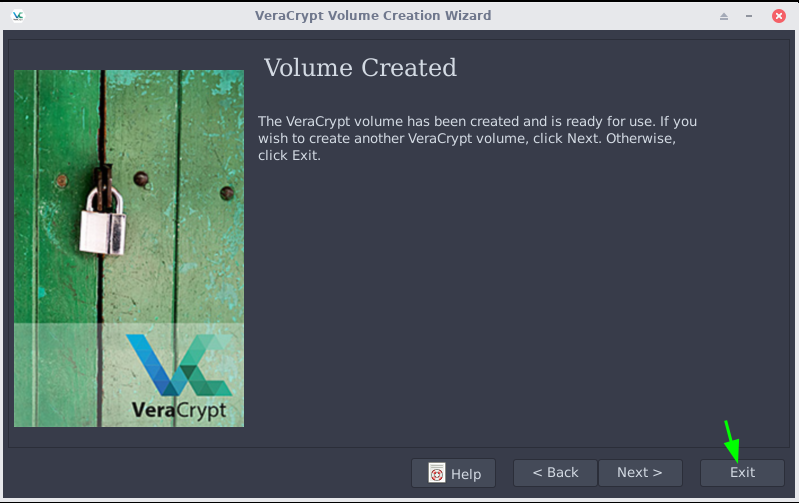
ONLY THEN the veracrypt volume is completed, and can be backed up somewhere else:
-copy it to your mainpc, laptop, homeserver and phone
-copy it to a usb key, which is to be hidden somewhere
-hide it in plain sight using steghide inside of a very large image.
Now let's take a look at how this looks like once it's applied:
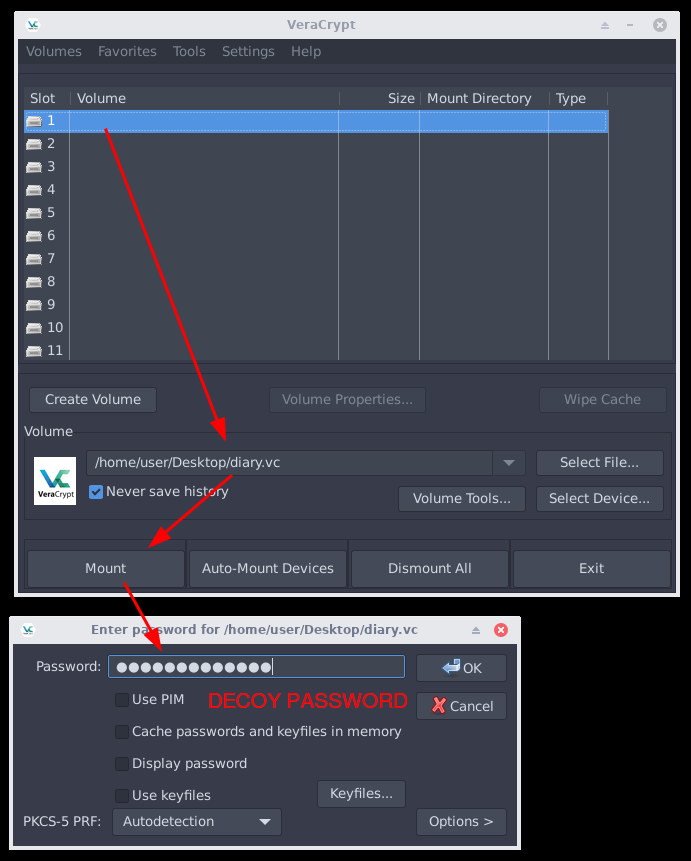
First we open the hidden volume:
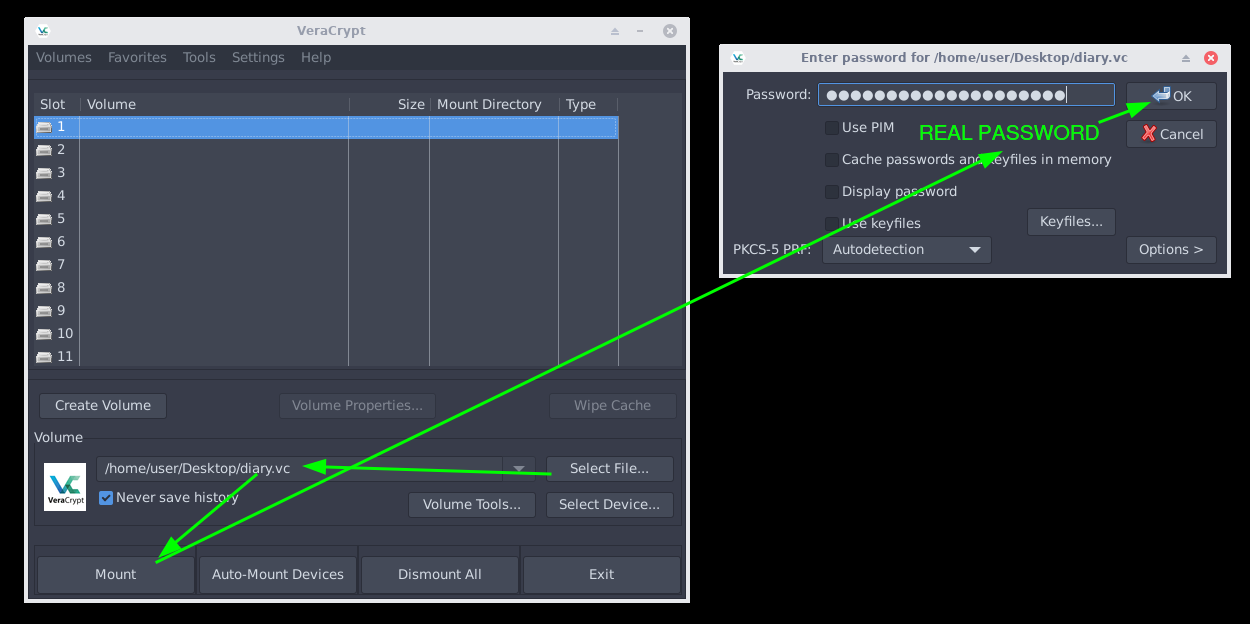
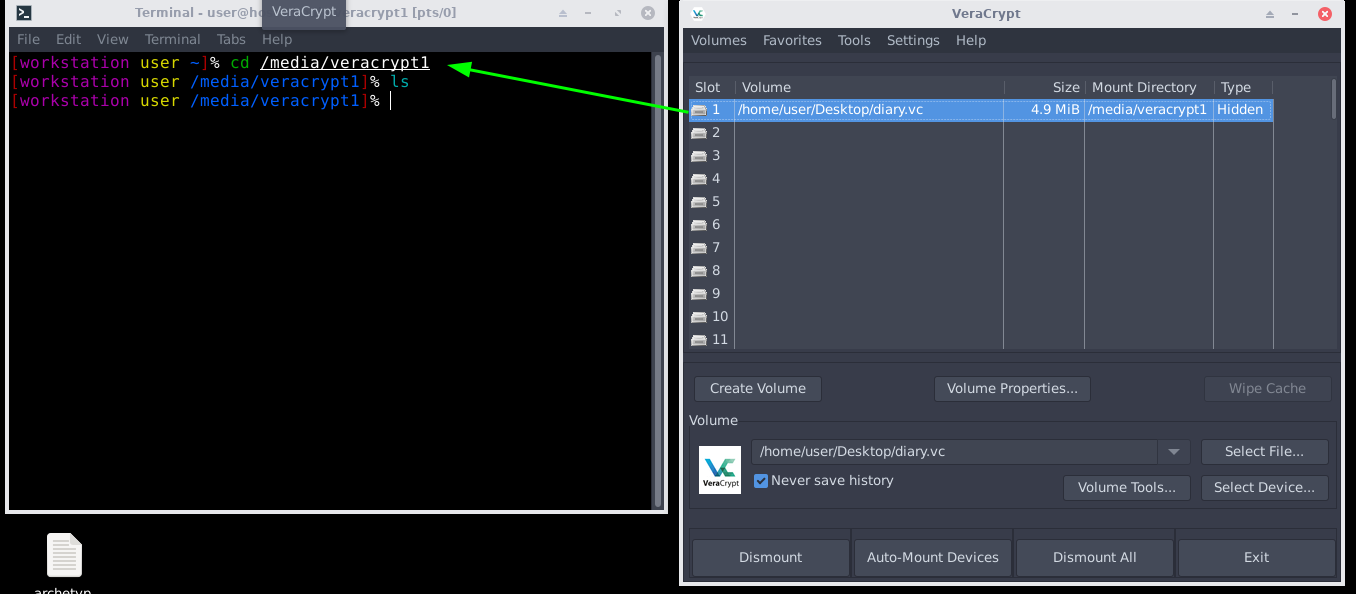
Backup all of your critical data (ssh config, ssh keys, pgp keys, keepass .kdbx files, etc.) (max size= 10Mb)
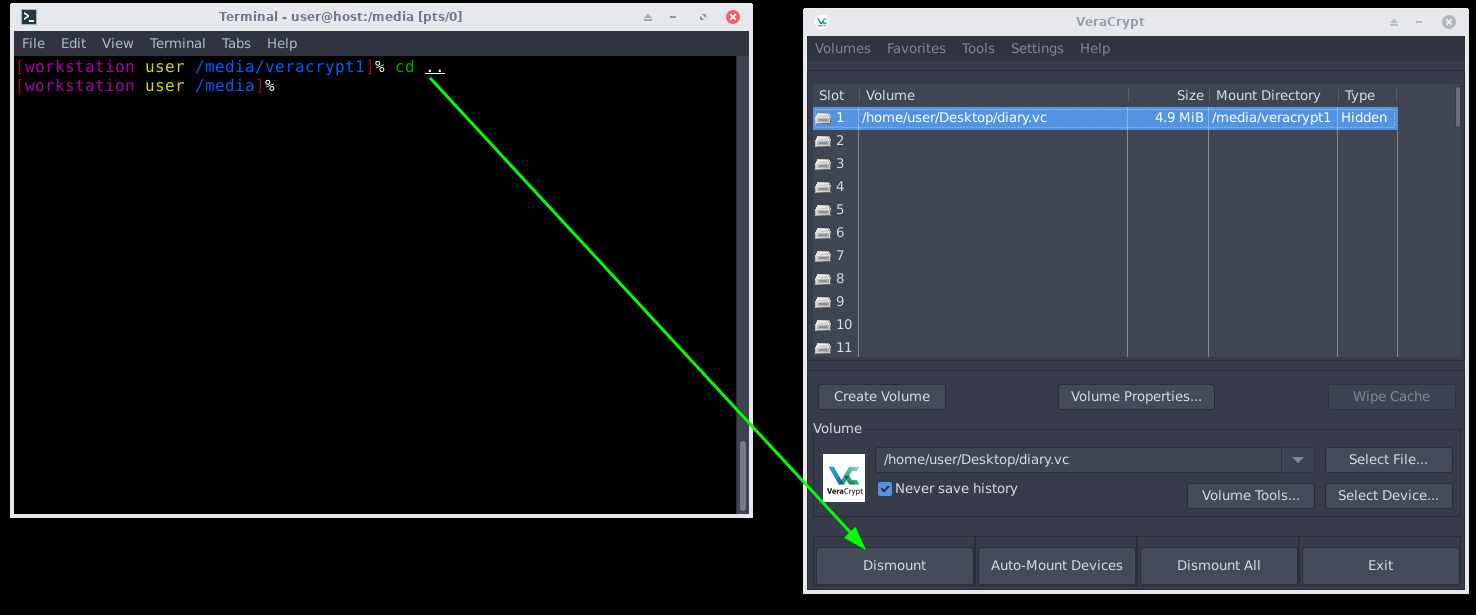
Then close the hidden volume:
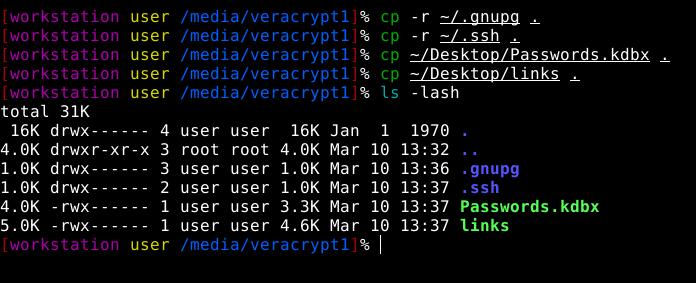
Open the decoy volume of the veracrypt volume diary.vc
write something in there such as your week in a small text file, name it with today's date. (don't reveal the presence of a hidden file in the text content). This is just an example as to what content you could put there. Goal is that the content must make sense in case if you're forced to type in your password there. Second goal is that for each veracrypt hidden volume changes that occur, the content of the decoy partition must also change because otherwise it will reveal the existance of the hidden volume if the remote server keeps the previous versions of each file.
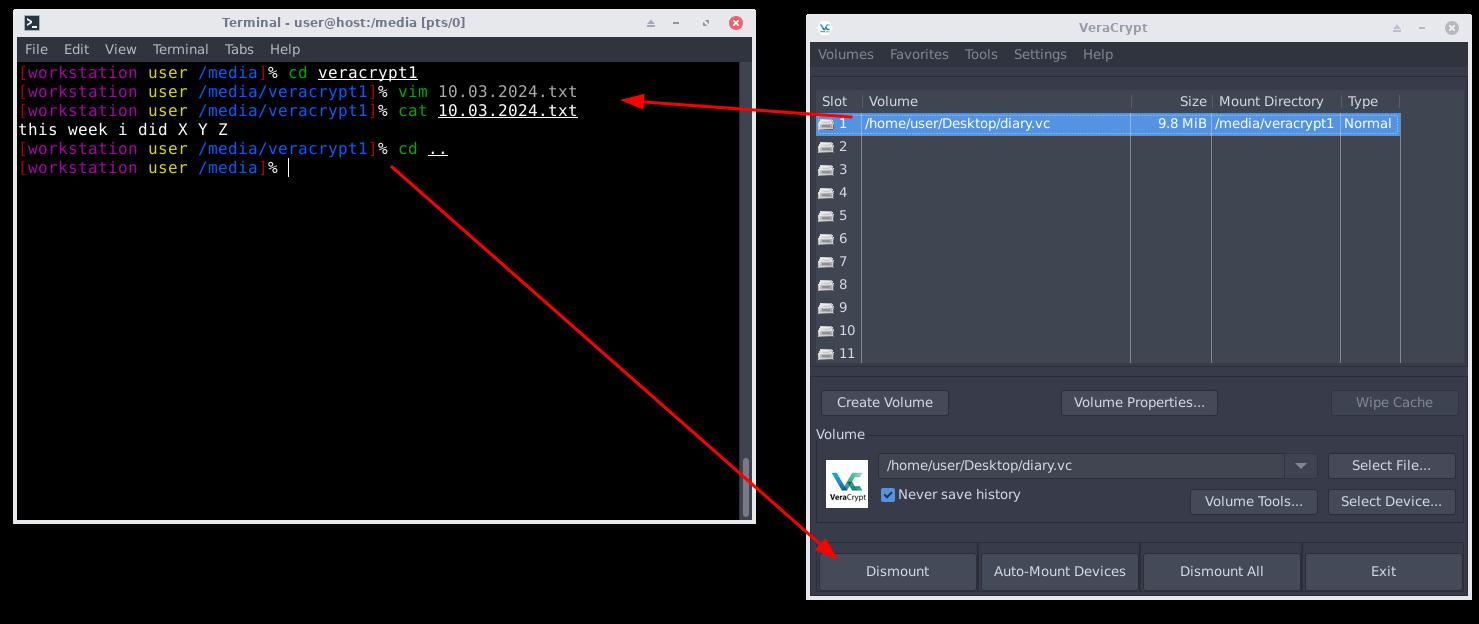
Once you have closed the decoy volume, the veracrypt volume is ready to be backed up:
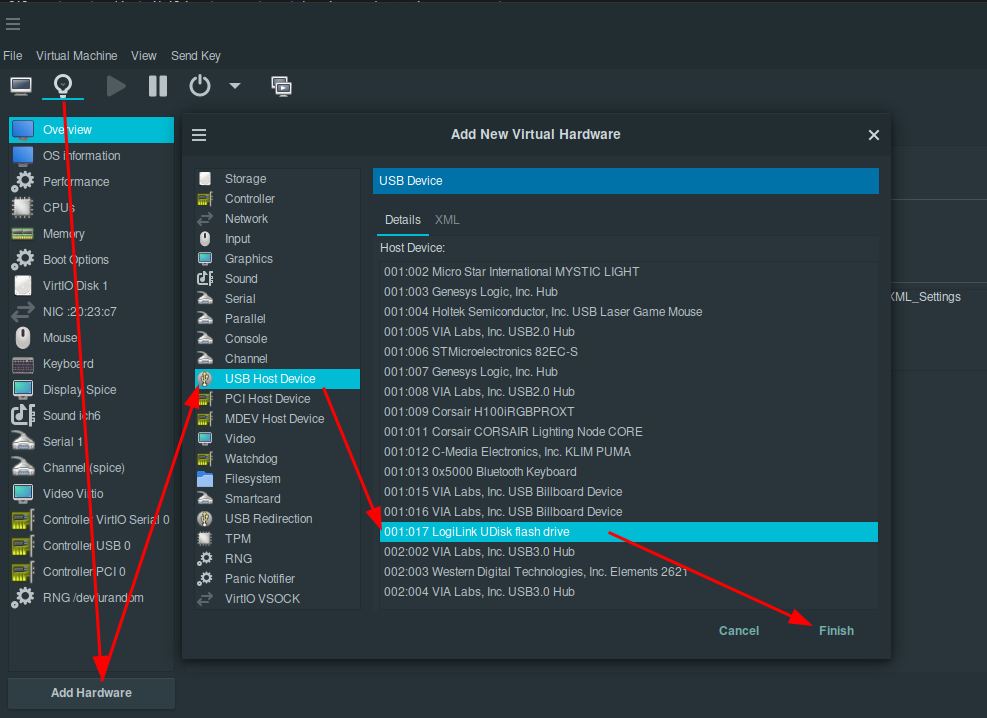
copy it to a server (wherever you want online), and then copy the file on your mainpc, your laptop and then you can also put it on a usb key to be hidden somewhere.
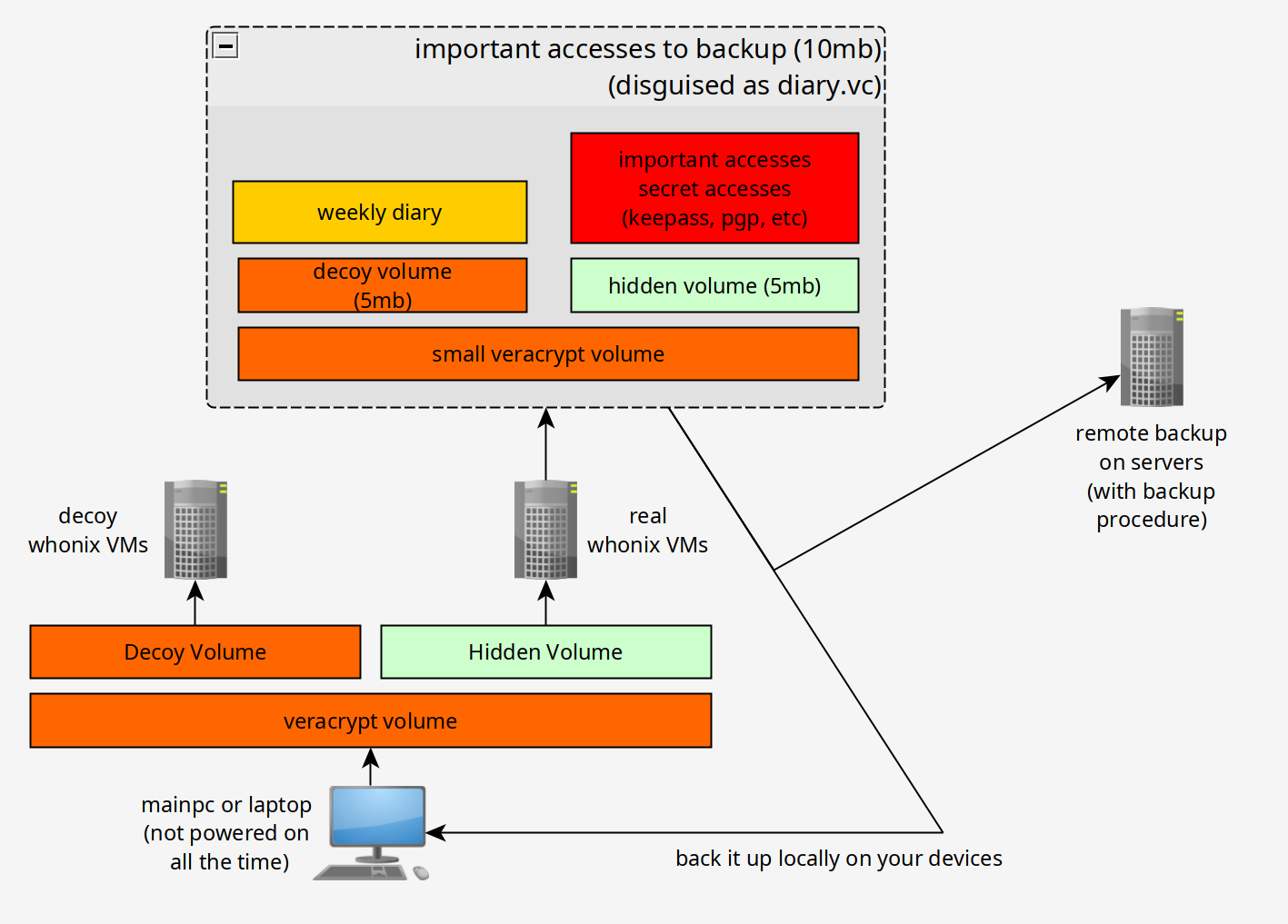
Like so you're covered in case if you are forced to give away your password, and in case if an adversary fills the decoy partitions of your veracrypt volumes in an attempt to destroy the hidden partitions.
You can get creative as to how you choose to hide the veracrypt volume aswell, such as replacing a random linux binary in the /bin/ folder, or a library in /lib, or a file in /etc/, burying the usb key somewhere underground, etc
Until there is Nothing left.
Donate XMR: 8AUYjhQeG3D5aodJDtqG499N5jXXM71gYKD8LgSsFB9BUV1o7muLv3DXHoydRTK4SZaaUBq4EAUqpZHLrX2VZLH71Jrd9k8
Contact: nihilist@nihilism.network (PGP)